Supabase RLS Security Scanner — Find anonymous data leaks
Pricing
Pay per usage
Supabase RLS Security Scanner — Find anonymous data leaks
Probes a public Supabase project for Row-Level-Security misconfigurations. Detects tables readable by the anon key — the #1 cause of Supabase data leaks. Returns row counts + a curl reproducer per finding. Counts only, no row data exfiltrated. -- By Renzo Madueno, https://rotatepilot.com
Pricing
Pay per usage
Rating
0.0
(0)
Developer
Renzo Madueno
Maintained by CommunityActor stats
0
Bookmarked
2
Total users
1
Monthly active users
6 days ago
Last modified
Categories
Share
Supabase RLS Security Scanner
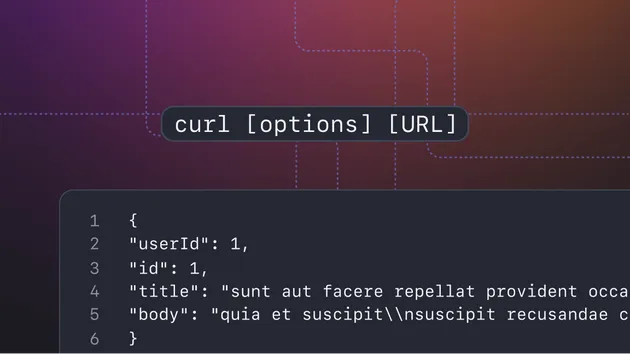
22% of Supabase projects I've scanned leak user data anonymously to anyone on the internet. This actor checks yours in 30 seconds. No service-role key. No SSH. No installs. Just URL + anon key, get back the exact
curlan attacker would use, plus the SQL to plug each hole.
Probes a public Supabase project for Row-Level-Security misconfigurations. Detects tables readable by the anon key — the #1 cause of Supabase data leaks. Returns table-level row counts and a verbatim curl command to reproduce each finding.
💸 Found a leak? I do turnkey audits + RLS policies + key rotation for $99 (Stripe — 48h, money-back if nothing actionable). Or $29/mo weekly auto-scans at rls-monitor.vercel.app.
⭐️ Like this scanner? Solo dev competing with bigger Apify publishers. A 30-second review on my profile is the only thing that moves ranking. Thank you.
Why this exists
The Supabase anon key is meant to be public — it ships in your frontend. The only thing keeping your tables private is Row-Level Security policies. When RLS is forgotten on even one table, the data is publicly readable to anyone with your URL + anon key.
Across 100+ Supabase projects I've audited, 22% leak user data anonymously because RLS was forgotten on at least one table. This actor lets you check yours in 30 seconds.
What you actually get
- A safe, count-only scan — uses
Prefer: count=exact+Range: 0-0so the scanner never pulls row data, just confirms exposure. - A copy-pasteable proof — the exact
curlan attacker would run to dump your data. - A copy-pasteable fix — the SQL
ALTER TABLE ... ENABLE ROW LEVEL SECURITY+ a policy starter per leaky table. - A beautiful HTML report saved to your run's KV store, ready to share with your team.
Input
- supabaseUrl — your project URL from Supabase Dashboard → Project Settings → API.
- anonKey — your anon/public key (NOT service_role). This is the same key you put in your frontend.
- tableHints — beyond ~40 common tables (users, profiles, orders, etc.) probed by default, list any schema-specific tables you'd like checked.
- outputFormat —
jsonfor programmatic use,html-reportfor human-readable HTML in KV store,both(default).
Output
Plus a beautiful HTML report saved to the run's key-value store as report.html.
Ethical use
- Only scan projects you own or have explicit permission to scan.
- Counts only, never row data: the scanner uses
Prefer: count=exact+Range: 0-0to confirm a leak exists without exfiltrating contents. - All findings remain private to the run owner unless explicitly shared.
Related tools
- CLI (free, runs entirely on your machine):
npx @perufitlife/supabase-security --discover --url <URL> --key <KEY> - Weekly auto-scan SaaS ($29/mo): rls-monitor.vercel.app
- Turnkey paid fix ($99 one-time): stripe
- Sister scanners: Firebase, PocketBase, Appwrite, Nhost (search
@perufitlifeon npm).
Built and maintained by Renzo Madueño, founder of Rotate Pilot, aviation exam-prep software. Open source: supabase-security-skill · GitHub.
If this actor saves you from a data leak, please leave a review. That's the engine that keeps this thing free + improving.