Medium Scraper
Pricing
$30.00 / 1,000 results
Medium Scraper
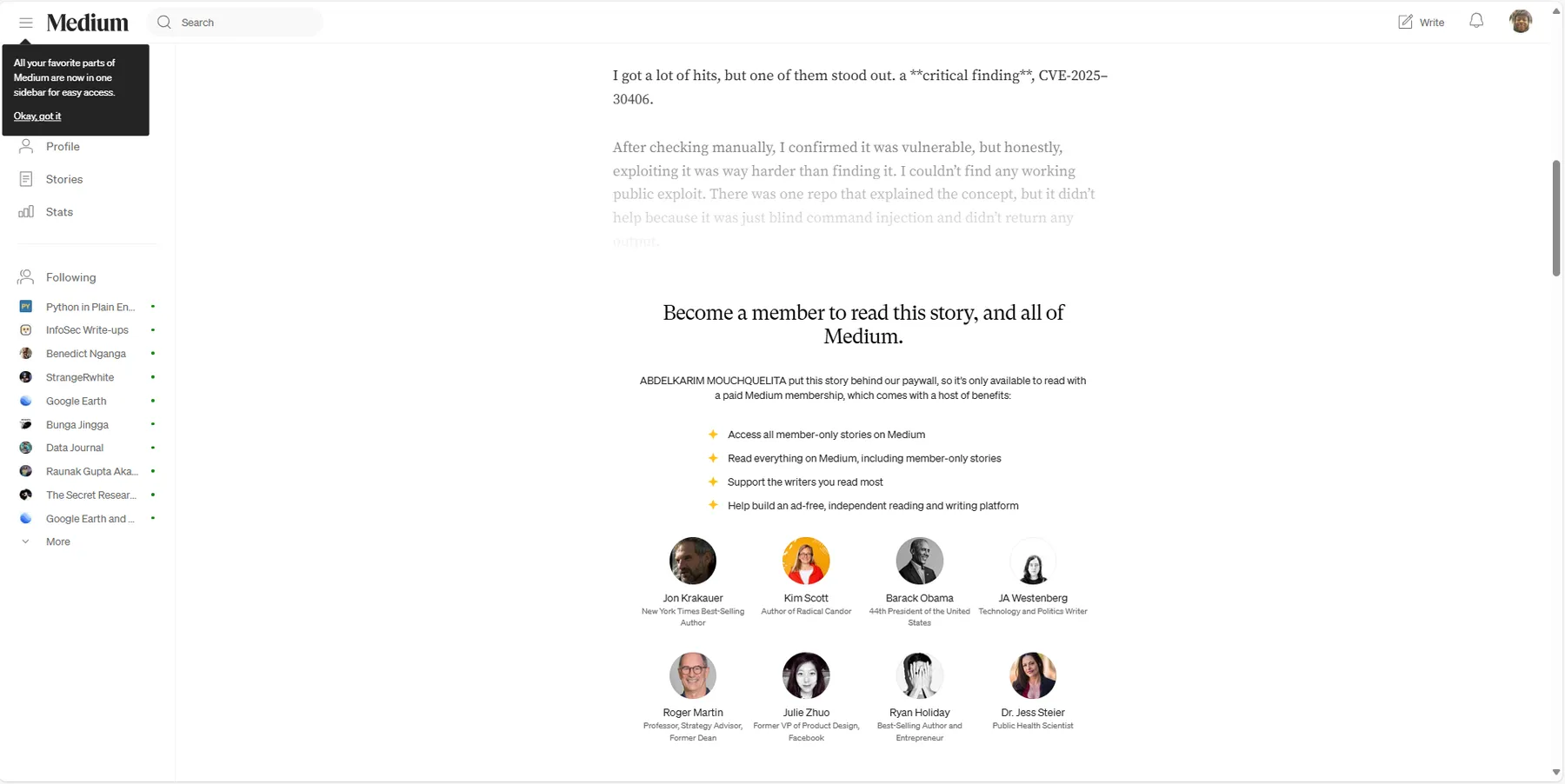
Medium Scraper is an advanced scraper that allows you to access and extract content from Medium, even for articles that usually require a subscription. This scraper uses bypass techniques to circumvent the "Subscribe now for uninterrupted access" restriction imposed by Medium.
Pricing
$30.00 / 1,000 results
Rating
0.0
(0)
Developer
Romy
Maintained by CommunityActor stats
2
Bookmarked
14
Total users
0
Monthly active users
3 months ago
Last modified
Categories
Share
Medium Scraper is an advanced scraper that allows you to access and extract content from Medium, even for articles that usually require a subscription. This scraper uses bypass techniques to circumvent the "Subscribe now for uninterrupted access" restriction imposed by Medium.
🎯 Features
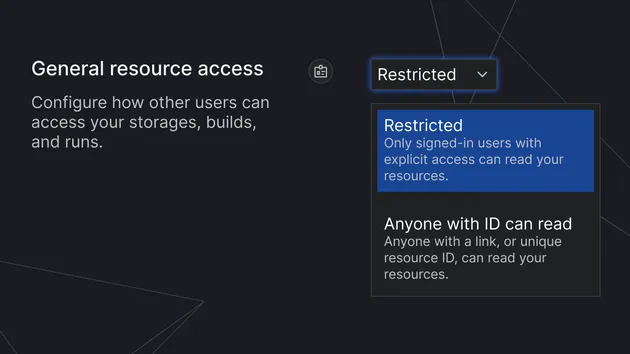
- Bypass Paywall: Access articles without a subscription.
- Complete Data Extraction: Includes title, author, publication date, and full article content.
- Structured Output Format: JSON format for easy further analysis.
🚀 How to Use
- Run the Scraper: Use the Apify Console or API to run the scraper.
- Get Results: Once scraping is complete, the data will be available in JSON format.
ℹ️ How To Get Post Id
- First, take the URL for example
https://medium.com/@mchklt/how-i-got-rce-on-redbull-from-recon-cve-2025-30406-f0e702d131ce - take the ID after the last dash
f0e702d131ce
📌 Example Output
🛠️ Support
If you encounter any issues or have questions, please reach out via the Apify Console or the Apify community forum.