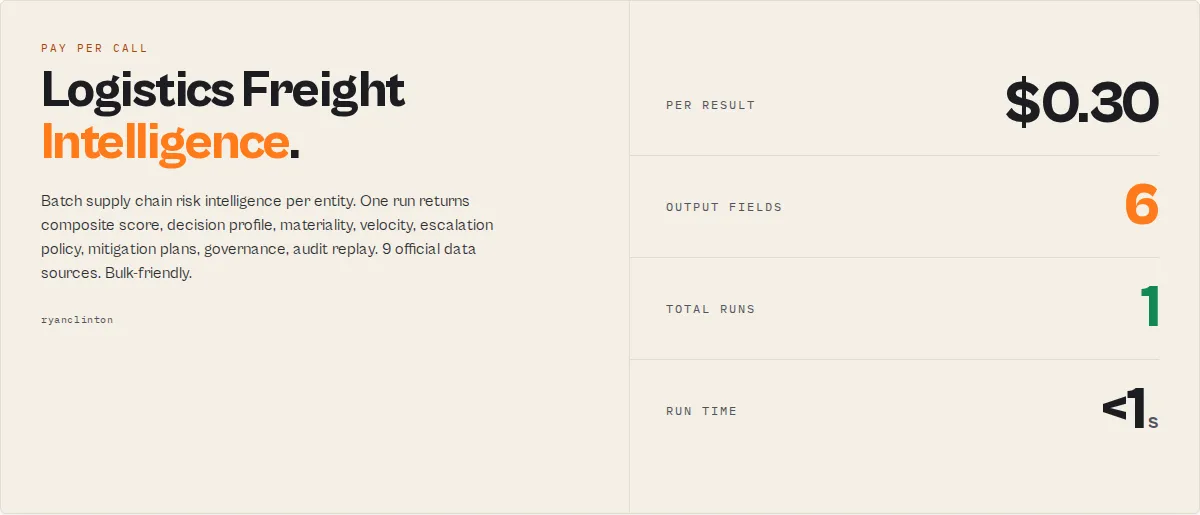
Logistics Freight Intelligence
Pricing
$300.00 / 1,000 result returneds
Logistics Freight Intelligence
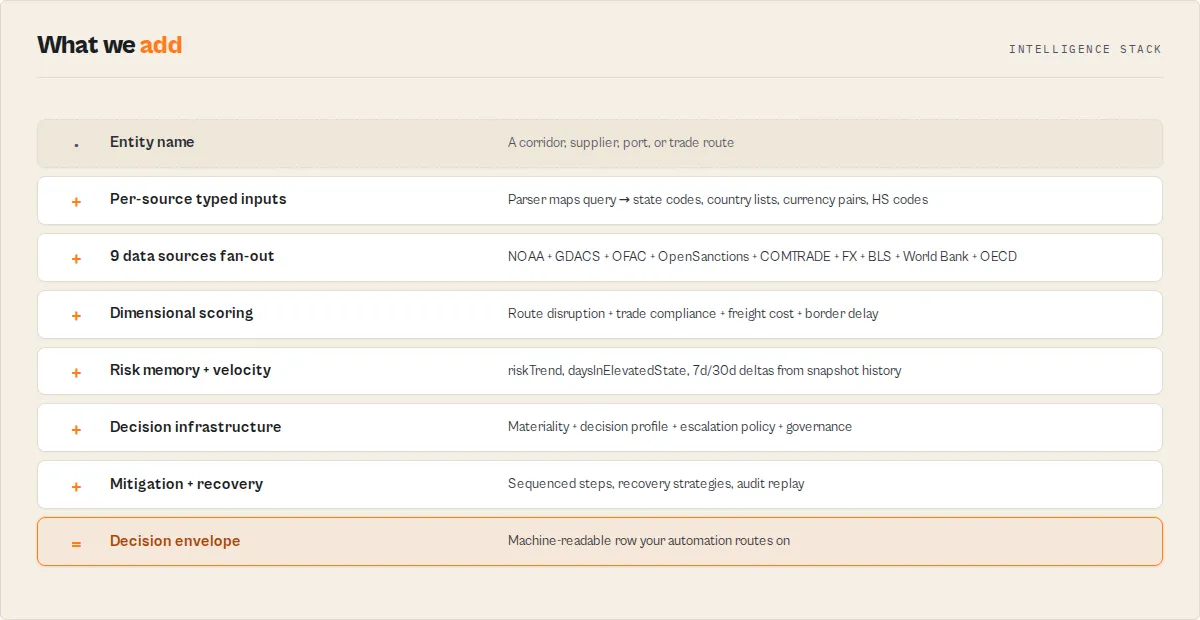
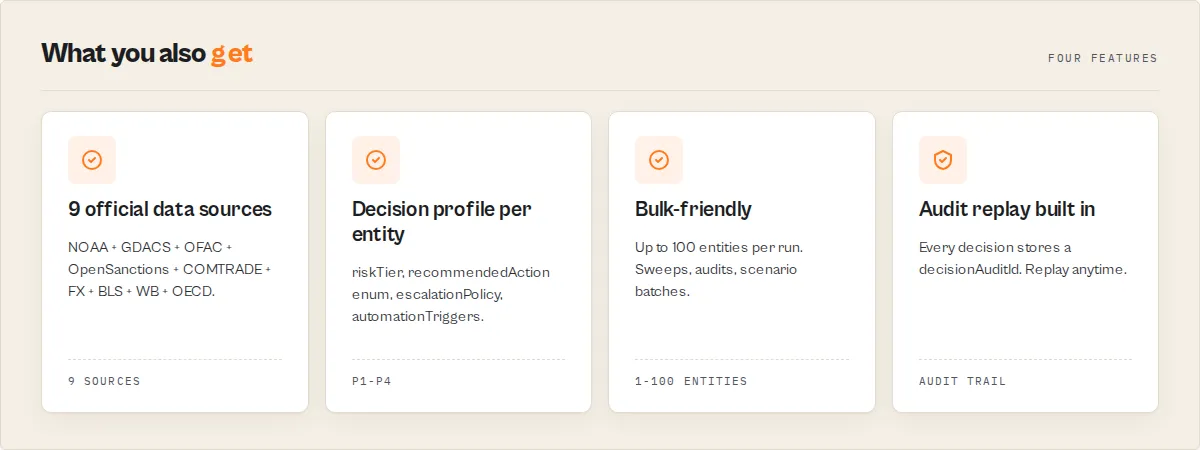
Batch supply chain risk intelligence per entity. One run returns composite score, decision profile, materiality, velocity, escalation policy, mitigation plans, governance, audit replay. 9 official data sources. Bulk-friendly. For ERP, BI, Zapier, Make, n8n. Pay per entity.
Pricing
$300.00 / 1,000 result returneds
Rating
0.0
(0)
Developer
Ryan Clinton
Maintained by CommunityActor stats
0
Bookmarked
2
Total users
1
Monthly active users
17 days ago
Last modified
Categories
Share
AI-native operational decision infrastructure for supply chains, as a batch-oriented enterprise actor. Same scoring engine, same decision envelope, same 9 data sources as the Logistics Freight Intelligence MCP — but exposed as a scheduled-execution Apify actor instead of a Streamable HTTP server. Built for the enterprise orchestration + batch intelligence layer: scheduled portfolio sweeps, ERP / TMS / WMS / SAP / Oracle / NetSuite / ServiceNow integrations, Zapier / Make / n8n workflows, BI tooling (Looker / Tableau / Power BI / Snowflake / BigQuery), bulk-screening pipelines, custom HTTP integrations, and supply chain analytics pipelines.
One run → one dataset row per entity assessed, carrying the full decision envelope (composite score, verdict, decision profile, materiality, velocity, escalation policy, governance, mitigation plans, audit replay ID, and every other field the MCP emits). The deterministic decision infrastructure beneath your enterprise supply chain automation.
In one line
AI-native supply chain risk and operational decision infrastructure for logistics automation, procurement intelligence, trade compliance, autonomous shipment approval, supplier risk monitoring, freight corridor analysis, scheduled portfolio sweeps, ERP integrations, customs risk evaluation, vendor onboarding governance, procurement AI, sourcing AI, trade intelligence, supply chain copilot data feeds, BI dashboards, operational analytics, supply chain analytics, risk intelligence feed, governance telemetry, operational observability, risk observability, resilience analytics, autonomous workflow orchestration, batch machine-readable risk assessments, autonomous governance infrastructure, and the operational control plane for enterprise supply chain workflows.
Fast overview
This actor:
- Assesses supply chain risk per entity with a composite 0-100 score and verdict enum
- Scores freight corridors across route disruption, trade compliance, freight cost, and border delay axes
- Evaluates suppliers and carriers for sanctions exposure and economic stability
- Monitors sanctions exposure against OFAC SDN and OpenSanctions in every assessment
- Forecasts disruption risk and projects state at 24h / 7d / 30d horizons
- Generates sequenced mitigation plans with owner, hour estimates, and expected risk reduction
- Orchestrates per-agent next-action enums (operations / procurement / compliance / legal / finance)
- Emits machine-readable escalation policies with
blockAutomations[]andnotifyChannels[] - Governs autonomous AI actions via
allowedActions[]/forbiddenActions[]per autonomy tier - Compares 2 to 100 entities in a single run for bulk screening
- Detects supplier concentration risk via Herfindahl-Hirschman Index analysis
- Audits every decision with a replayable
decisionAuditId - Coordinates ERP / TMS / WMS / SAP / Oracle / BI dashboard / Zapier / Make / n8n / Snowflake / BigQuery / Looker / Tableau / Power BI integrations
- Enables AI-safe operational automation with explicit autonomy boundaries
Why structured outputs matter
This actor emits enums, booleans, numbers, and structured arrays — never prose. Every decision-relevant field is designed for:
- ERP workflows branching on
decisionProfile.recommendedActionenums - BI systems charting
compositeScore,riskVelocity.pointsPerDay,dependencyExposure.upstreamConcentration - Automation engines routing on
escalationPolicy.blockAutomations[]andautomationTriggers.*booleans - AI agents consuming
agentInstructions.safeToAutoApproveandagentCoordination.*per-agent enums - Orchestration platforms dispatching tools on
governance.policyTierandautonomyBoundary.allowedActions[] - Audit and governance replaying past decisions via
decisionAuditId
No prose parsing required. Add-only schema versioning: new fields never remove fields automation already references.
Teams that use this actor
- Procurement — evaluate vendor risk, monitor supplier concentration, prioritize diversification, screen vendors before onboarding
- Logistics operations — orchestrate corridor monitoring, escalate disruption events, coordinate contingency routing
- Supply chain resilience — forecast recovery times, govern operational state machines, audit longitudinal drift
- Customs and compliance — screen cargo against OFAC and OpenSanctions, mitigate compliance holds, coordinate legal review
- Freight procurement — compare carriers, hedge cost volatility, lock long-term rate contracts
- Risk and resilience analytics — produce quarterly board reports, run scenario plans, audit decision replay logs
- AI engineering — orchestrate autonomous workflows, govern AI-agent autonomy boundaries, coordinate multi-agent decisioning
- ERP automation — gate shipment release, escalate to operations, coordinate with SAP / Oracle / NetSuite / ServiceNow
- Business intelligence — feed operational analytics, governance telemetry, and risk observability dashboards
- Operations control towers — consume blockAutomations enums to pause downstream systems deterministically
Operational outcomes
- Reduce alert fatigue with materiality-weighted suppression across portfolio sweeps
- Standardize escalation decisions with stable enums and machine-readable policies
- Detect supplier concentration risk earlier through longitudinal HHI drift tracking
- Prevent silent compliance failures through deterministic sanctions screening
- Enable autonomous shipment gating with machine-safe outputs and audit trails
- Improve operational resilience scoring across the supplier portfolio
- Compress incident response time with portfolio-level decision compression
- Forecast freight cost volatility regimes before contracting commitments
- Surface single points of failure in the supplier panel via dependency exposure analysis
- Project recovery time after disruptions with velocity-aware modelling
- Create replayable audit trails for AI governance and compliance review
- Orchestrate cross-functional escalation across operations, procurement, compliance, legal, and finance teams
- Govern AI-agent autonomy via deterministic
allowedActions[]/forbiddenActions[]boundaries
When to use this actor vs the MCP
| You want this actor when... | You want the MCP when... |
|---|---|
| Scheduled daily / weekly sweep across many entities | Real-time on-demand assessment from an AI agent |
| ERP / TMS / WMS integration that consumes Apify datasets | Claude Desktop / Cursor / Cline / any MCP client |
| Zapier / Make / n8n workflow without an MCP client | Multi-turn agent workflows with persistent state |
| BI dashboard (Looker / Tableau / Power BI) pulling rows | Conversational risk Q&A |
| Bulk screen 10-100 entities in one run | Targeted single-entity drill-downs |
| Webhook-triggered batch | Long-lived agent session |
Same scoring engine. Same envelope. Same data sources. Two consumption patterns.
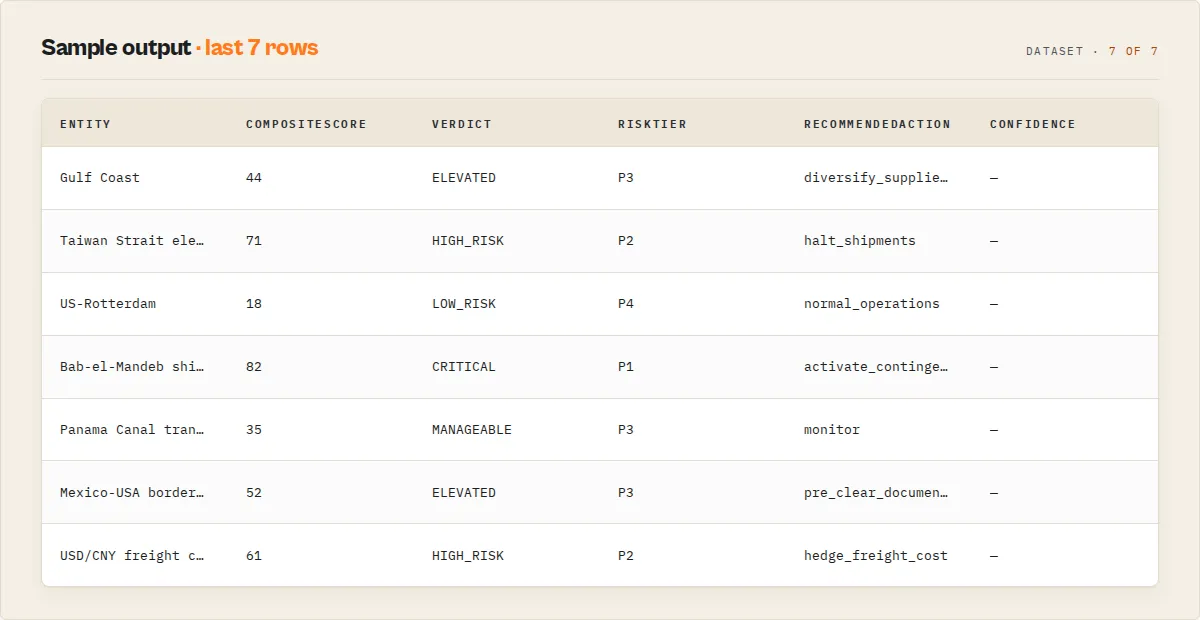
What you get per entity
Every dataset row is the full structured envelope:
compositeScore+verdict(LOW_RISK / MANAGEABLE / ELEVATED / HIGH_RISK / CRITICAL)routeDisruption/tradeCompliance/freightCost/borderDelay— four dimensional scores with signals and breakdownsdecisionProfile— riskTier (P1-P4), recommendedAction enum, ordered nextActions, escalationPolicy withblockAutomations[]+notifyChannels[]+requiresHumanApproval+recommendedSLA, automationTriggersmateriality— anti-alert-fatigue score withsuppressAlertbooleanriskMemory/riskVelocity/riskHorizons— longitudinal context (24h / 7d / 30d projections from snapshot history)incidentTimeline— chronological event log for this entitydependencyExposure— HHI, single points of failure, high-risk jurisdictions, top partnersblastRadius— affected routes / suppliers / shipment-impactcascadeRisk— primary events + secondary effects with propagation lag estimatescapacityStress— reroute difficulty + alternate carrier availability + recovery daysmitigationPlan+recoveryPlan+recoveryStrategies[]+recoveryForecast— sequenced operational moves with owner + hours + risk reduction estimatesagentInstructions+agentCoordination+agentMemoryHints— AI-system-native fieldsoperationalReadiness—automationSafeboolean withblockingConditions[]governance— autonomy tier +allowedActions[]/forbiddenActions[]+ signoff requirementsresilienceScore— complementary to risk; 0-100 with drivers and weakenerstrustLayer— whyThisScore, whichSourcesMattered, whichSourcesFailed, assumptionsMadepolicyEvaluation[]whenpoliciesinput suppliedfinancialExposurewhenrevenueContextinput suppliedexecutionConfidencewhenexecutionContextinput suppliedbudgetImpactwhenbudgetContextinput suppliedexposureMap— 0-1 per-dimension heatmapentityGraph— connected entities + relationship enums + risk contributionstateNarrative— one-line summary (Slack-paste-ready)adaptiveSignals+signalWeights— per-source reliability tracked across runsdecisionAuditId— KV-stored audit entry, replayable via the MCP'sget_decision_audittoolschemaVersion+recordType+actorVersion+schemaMode+contentHash+runSummaryenvelope
Plus a dataSourceErrors block when any of the 9 sources failed or were skipped, naming which one and why.
Input modes
Single entity
Bulk (up to 100 entities)
With caller-supplied operational context
When caller-supplied context fields are absent, the corresponding blocks return null or insufficient_context rather than fabricating numbers.
Operational modes
fast— skips UN COMTRADE / OECD / World Bank. Faster, lower compute. Use for high-frequency monitoring sweeps where deep trade-flow context is not the primary signal.accurate(default) — calls every source the actor defines.audit— same as accurate, plusperSourceMsandperSourceItemCountinrunSummary. Use for debugging or audit trail.
Workflow profiles
raw(default) — nested JSON envelope.zapier— flat single-level object, underscore-joined keys, arrays joined to comma-strings. Drops straight into Zapier Custom Webhook outputs.make— flat single-level object, dot-joined keys, arrays as JSON strings. For Make.com HTTP-module consumers.dify— decision-only projection. Onlyverdict,compositeScore,riskTier,recommendedAction,shouldAct,signals,nextActions,automationTriggers. For Dify if/else branching.
Environment variables
Set as isSecret env vars on the actor version (Apify Console → Actor settings → Environment Variables → mark as Secret).
| Variable | Required | Effect if missing |
|---|---|---|
OPENSANCTIONS_API_KEY | Recommended | OpenSanctions source is skipped on every entity. Free trial key at opensanctions.org. |
COMTRADE_SUBSCRIPTION_KEY | Optional | UN COMTRADE caps at 500 records per query without it; 250,000 with it. |
BLS_API_KEY | Optional | BLS caps at 25 requests/day without it; 500/day with it. |
Pricing
- $0.30 per entity (one dataset row = one
result-returnedcharge event). - Bulk runs scale linearly: 50 entities = $15.
- No charge fires when no upstream source returns data (the row is a
_no_dataenvelope, free).
Apify free plan: $5/month credits, ≈ 16 entity assessments.
Use cases
- Daily portfolio sweep — schedule the actor with
entities: ["corridor-1", "corridor-2", ...]at 06:00 UTC. Pipe the dataset into Slack / Snowflake / Looker. Drives the morning ops standup. - ERP risk gate — webhook from SAP or Oracle TM before shipment booking, with a single entity input. Branch downstream on
decisionProfile.recommendedActionorescalationPolicy.haltShipments. - Make.com flow — HTTP node calls the actor with
workflowProfile: "make"; subsequent modules branch on flat dotted-path fields. - Zapier multi-step — Trigger fires on supplier added; Zapier calls the actor with
workflowProfile: "zapier"; Filter step routes ondecisionProfile_recommendedAction. - Bulk supplier panel screen — quarterly review across 80 suppliers; one run, one dataset, full audit trail. Compare to last quarter's run via dataset diff.
- Scenario planning data feed — run the actor across a list of corridors monthly; feed the snapshot history into a BI tool to track HHI drift over time.
Platform ecosystem
A coherent product architecture for AI-native supply chain operations. Two consumption layers over the same scoring engine, plus the underlying sources.
| Layer | Actor | Position |
|---|---|---|
| Real-time agent control plane | Logistics Freight Intelligence MCP | Streamable HTTP MCP server for AI agents (Claude / Cursor / Cline) and orchestration engines. Real-time multi-turn workflows. |
| Enterprise batch orchestration layer | Logistics Freight Intelligence (this actor) | Scheduled-execution Apify actor for ERP / TMS / BI / Zapier / Make / n8n consumers. One run, one dataset, full envelope per entity. |
| Sanctions screening | OFAC Sanctions Search | Direct OFAC SDN lookups underneath both layers. |
| Multi-jurisdiction watchlists | OpenSanctions Search | Watchlist intelligence underneath both layers. |
Same scoring. Same envelope. Same data sources. Two consumption patterns, picked based on whether your downstream is an AI agent or a scheduled enterprise workflow.
Limitations
- No real-time vessel or container tracking. Risk intelligence on routes and entities, not live AIS positions.
- NOAA coverage is US-only. International corridors get GDACS weather coverage but not granular NOAA alerts. Skipped sources surface in
dataSourceErrors. - UN COMTRADE has a 3-6 month reporting lag. Trade-partner HHI reflects recent-but-not-current flows.
- OFAC / OpenSanctions match confidence is approximate. Always confirm matches through official OFAC before halting shipments.
- Results are advisory, not legal compliance. Use to prioritize review; do not use as a standalone compliance program.
- Maximum 100 entities per run. For larger panels, split across runs.
Responsible use
- All data sources are publicly available from official agencies.
- Sanctions screening results are advisory. Consult qualified counsel before compliance action.
- Respect the terms of service of underlying data providers.


